Ledger Login
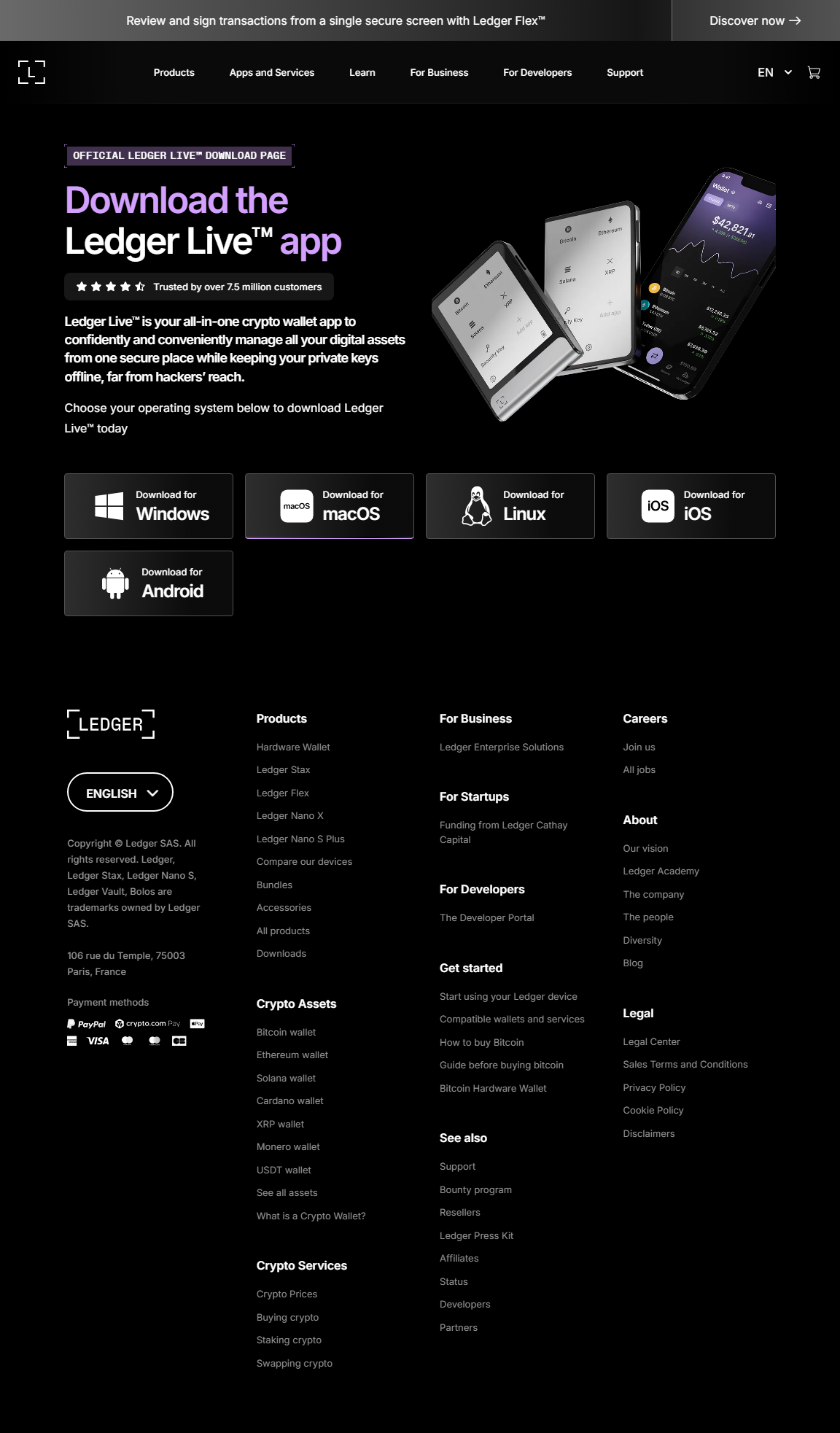
A complete guide to safely accessing, managing, and verifying your Ledger hardware wallet using Ledger Live — without ever exposing your private keys.
The concept of **Ledger login** is different from typical username-password systems. Ledger devices do not require account-based sign-ins.
Instead, the “login” process involves authorizing the Ledger Live app to securely communicate with your Ledger hardware wallet.
This unique approach ensures that your private keys and recovery phrase never touch the internet — solidifying Ledger as one of the strongest cold-storage solutions in the crypto world.
In this guide, you’ll learn exactly how the login flow works, how to connect the device, and how to maintain airtight security.
⚠️ Important Security Warning
Ledger will **never** ask for your 24-word recovery phrase during login.
If any site or app requests it, it is a phishing attempt.
Your Ledger device is the only place where your keys remain valid.
What Does “Ledger Login” Really Mean?
Ledger login refers to the authorization handshake between:
✔ Your Ledger Hardware Wallet (Nano S Plus / Nano X)
✔ The Ledger Live application
✔ A secure USB or Bluetooth connection
“With Ledger, you don’t log into crypto — your device unlocks it.”
A login flow rooted in cryptographic ownership, not cloud accounts.
How Ledger Login Works (Step-by-Step)
Below is the complete login flow when connecting your Ledger device to Ledger Live:
1. Open Ledger Live
Ensure it is the official version. Bookmarked links prevent phishing mistakes.
2. Connect Your Ledger via USB or Bluetooth
Nano X supports secure Bluetooth pairing; other models use USB-C.
3. Enter Your PIN on the Ledger Device
Entering your PIN unlocks local access; it never leaves the hardware wallet.
4. Open the Required App (e.g., Bitcoin, Ethereum)
Ledger Live will request permission, which you must approve manually on the device screen.
5. Confirm the Connection
This cryptographic handshake validates authenticity and completes the login.
Ledger Login vs Traditional Login
| Feature | Ledger Login | Traditional Login |
|---|---|---|
| Password Required | No | Yes |
| Private Key Exposure | Never | Possible |
| Hardware Authentication | Yes | No |
| Phishing Risk | Extremely Low | High |
Best Practices for Safe Ledger Login
- Use the official Ledger Live application only.
- Never type your recovery phrase online — login never requires it.
- Verify every transaction physically on the device screen.
- Enable Ledger Live’s password lock for local security.
- Keep firmware updated only through Ledger Live.
FAQ — Ledger Login
Does Ledger have a website login?
No. Ledger uses hardware-based authentication, not cloud accounts.
No. Ledger uses hardware-based authentication, not cloud accounts.
Can I log into Ledger without the device?
No — the hardware wallet is mandatory for all secure access.
No — the hardware wallet is mandatory for all secure access.
Is my PIN part of the login?
Yes. Your PIN unlocks your Ledger, but it is never transmitted.
Yes. Your PIN unlocks your Ledger, but it is never transmitted.
Can someone hack my Ledger login?
Only if they have your device *and* your PIN — otherwise impossible.
Only if they have your device *and* your PIN — otherwise impossible.
Ledger Login — Security Through Hardware
Ledger login is a radically secure approach that merges cryptographic authentication with physical verification.
No passwords, no online accounts, no risk of remote theft — just pure hardware-based authority.
With Ledger login, your digital wealth stays protected, offline, and entirely under your control.